True Hacktivism Isn’t for Sale: The Difference from Ransomware
I was a blackhat computer hacker as a young adult. I shared the popular belief that if I could break into it, it was the victim’s fault for having a vulnerable security posture, and there was a lesson to be learned from my attacks.
If it had an IP address, I could hack it. I attacked government websites and their internal networks across the globe, law firms, and even a satellite. I had my sights on the world and was determined to take it by storm, justifying every move I made because I had the power to judge the security postures across all industries.
This same mindset is foundational among many hacktivist groups today, especially among the ransomware gangs.
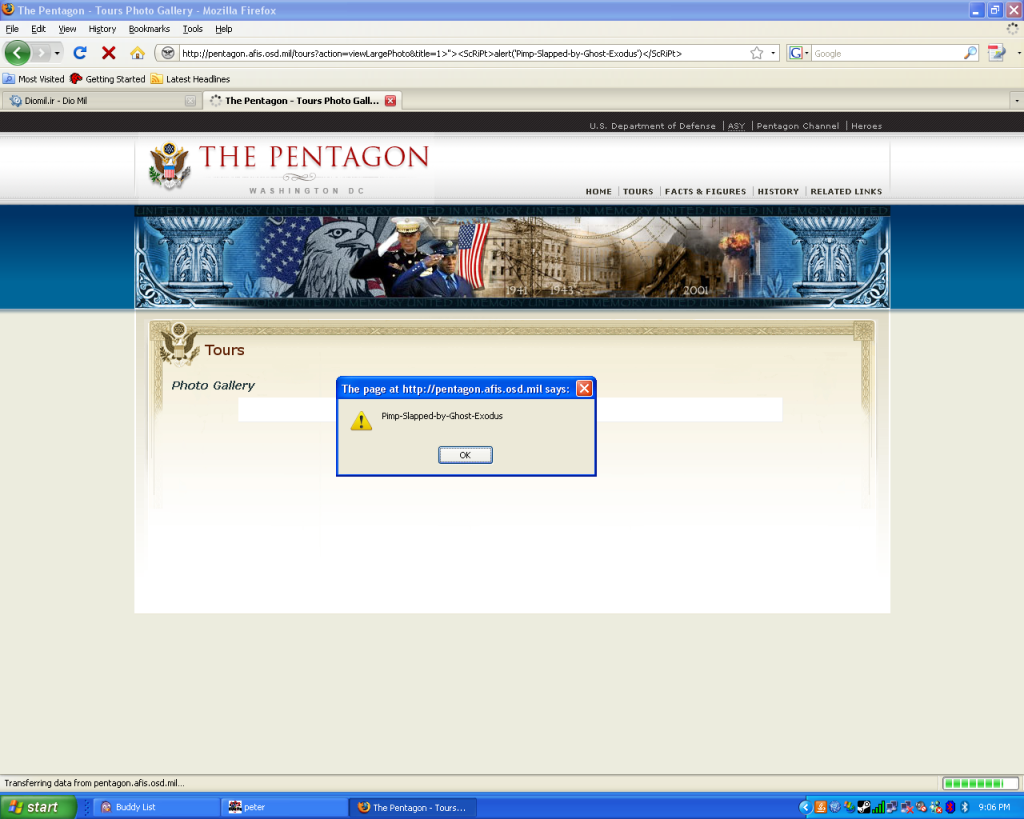
I even discovered a reflected cross-site scripting (XSS) vulnerability on the official Pentagon website, where I injected a simple alert box as proof-of-concept — more out of mischief than malice, just to show it could be done, and walked away unnoticed.
My reach into government systems was so extensive that even the FBI believed I had infiltrated a local police department, based on an interpretation of some screenshots I had, and an actual cybersecurity incident they were trying to piece together. They didn’t know about the Department of Homeland Security personnel who lived in my apartment complex whom I tried to honeypot for access to sensitive information, just to see if I could.
The thing is, I could have turned anything into a political or ideological motive. My pretext was, “the government should be competent enough to protect us from Chinese or North Korean threat actors.” But if I could do it, then China was doing it better — and not for fun.
I wasn’t stealing data or seeking profit. I was proving that I could. And if I could gain access, then bad actors more dangerous than me had probably already infiltrated the target. There was one case where this was true, where I had infiltrated an industrial control system, where I found myself contending for the system against Chinese hackers. In the end, I rationalized it as “just for fun” or “their fault for being vulnerable.”
Politically motivated ransomware groups often do the same thing. However, they hack, dump data, and extort, but frame the attack as “activism” or “justice” and then demand a “reward” in the form of extortion.
As a hacktivist from a bygone era, cut from the same cloth as my fellow hacktivists, we never sought justice for money. We had no ulterior motive besides seeking justice and having thrills.
Political Propaganda in Disguise
The line between hacktivism and cybercrime has always been blurred, since hackers must break laws in order to get their political message across. However, ransomware groups have turned that blur into a smoke screen to hide behind the thin veil of a cause.
They accomplish this by wrapping extortion in the language of politics, masking greed with the aesthetics of a rebellion. To those who don’t know better, it looks like a cause. But to those who aren’t fooled so easily, it's just branding.
Groups like DragonForce, Rhysida, SiegedSec, and Interlock always cloak themselves in political banners, claiming to fight imperialism, corruption, and oppression. Yet their actions tell competent audiences a different story by paralyzing hospitals, bleeding schools dry, holding governments and businesses hostage.
That is extortion dressed in the attire of ideology.
For example, DragonForce, the pro-Palestinian hacktivists turned RaaS group, operates like any other ransomware cartel. However, Handala Hack Team does not resemble typical ransomware groups like DragonForce. They aren’t motivated by money or chaos for the sake of making headlines and getting rich. They have a singular motive, and that is attacks on Israeli entities. That is their belief, and they uphold it, unlike the many others who just want money.
True hacktivism isn’t fueled by money.
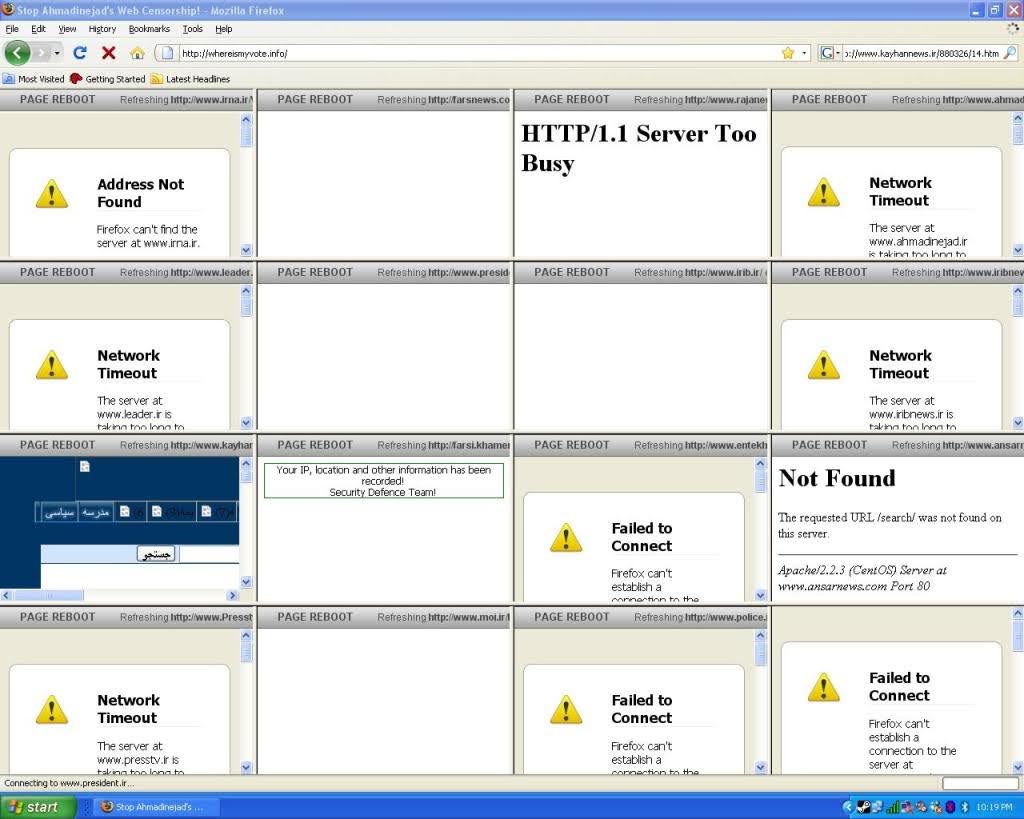
In June 2009, during the civil unrest known famously as the Green Movement, in Iran, during the aftermath of the Iranian Presidential elections, I was there in the trenches to support the protestors who, in outrage, claimed that President Mahmoud Ahmadinejad had stolen the election from his political opponent Mir-Hossein Mousavi.
Hacktivists launched a cyberwar, dismantling state-run media outlets like the IRNA (Islamic Republic News Agency), Fars News, Raja News, Kayhan, and others in a hailstorm of distributed denial-of-service attacks from around the world. We sabotaged censorship infrastructure by hammering Iran’s national filtering network, and built Tor bridges, SSH tunnels, and proxy servers for protesters to use during the dark days when the regime attempted to block nationwide access to Twitter.
For free.
That’s because true hacktivism isn’t for sale.