Job Platform Data Leak: 15K Users Exposed Due to S3 Misconfiguration

Researchers from leakd.com discovered a significant data leak involving the Amazon S3 bucket used by TechMeetups, a global network connecting startups, professionals, and developers. According to its website, the company organizes job fairs and collaborates with thousands of hiring companies.
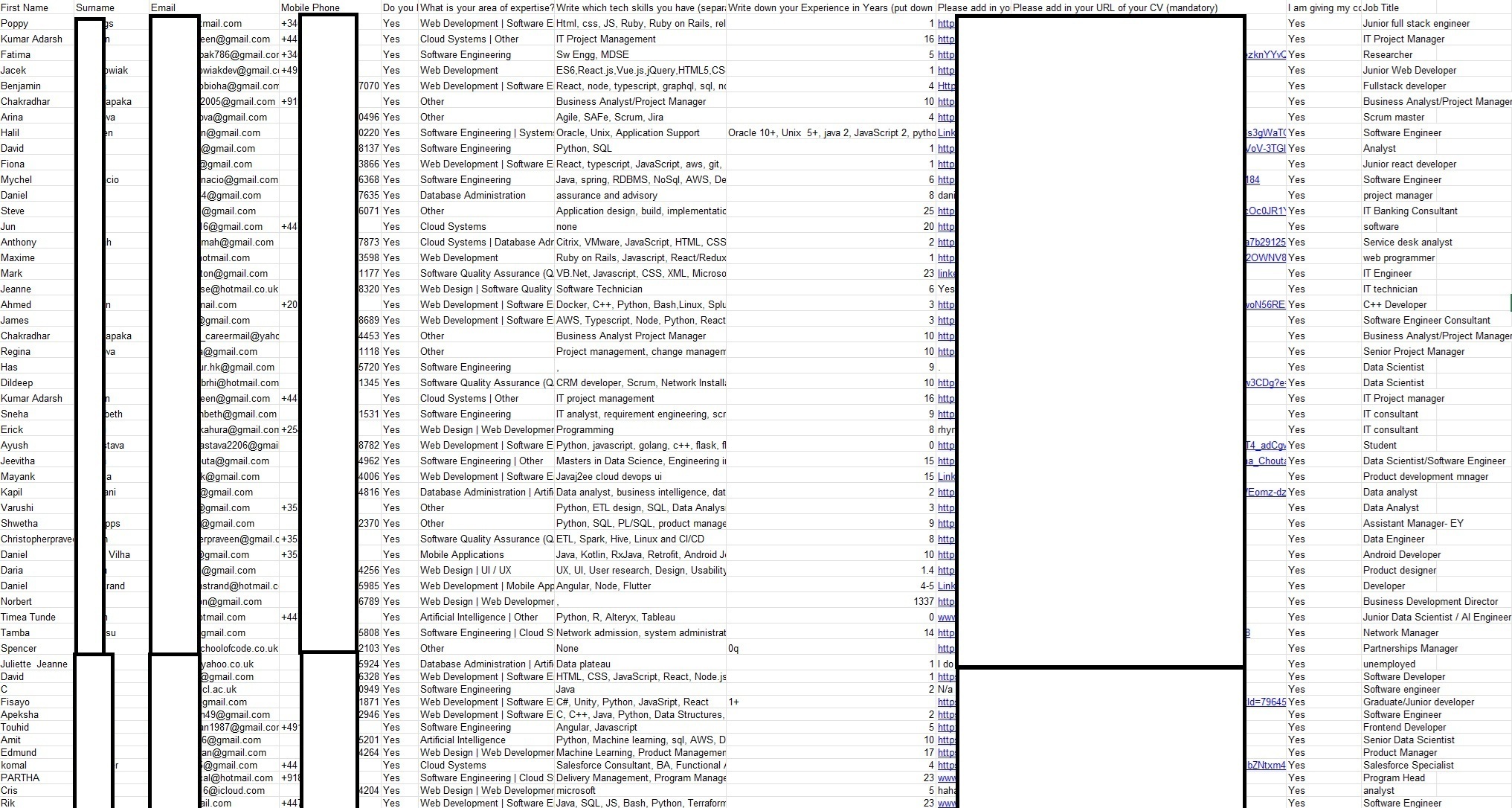
The misconfigured S3 storage left 15k sensitive files unprotected, which include the following:
- Emails
- Password hashes
- Full names
- Telephone numbers
- Social media profile links
- Resumés (CVs) totalling 60,000 records
- Applicant photos
Furthermore, the leak contained photographs of the applicants, mailing addresses, email addresses, phone numbers, social media contact details, citizenship status, personal remarks, and meticulously documented qualifications and employment history.
Moreover, there were screen recordings showing workflow desktop software used by the company, which displayed usernames, and a large trove of marketing material which not only further emphasizes the risk of identity theft, but also the theft of proprietary information, marketing strategies, and tools.
Consider the ramifications of the personally identifiable information contained in a job résumé. Aside from personal details, when such information is publicly exposed, it becomes easier for threat actors to impersonate victims—especially when dates of birth, mailing addresses, and other sensitive details fall into malicious hands.
Misconfigurations turn Malicious
S3 buckets are cloud storage containers that exist within AWS regions, where users store files. The service is used by major industries, including public sector organizations such as government agencies and defense contractors, as well as healthcare, tech companies, blockchain firms, small businesses, and individuals. Therefore, Amazon cloud storage is a prime choice for storage infrastructure.
However, even common S3 bucket misconfigurations such as improperly setting the bucket permissions on sensitive files to public will allow anyone across the web to list and download private files.
Also, not enabling S3 default encryption or server-side encryption allows bad actors to retrieve and read the data in plain text, and parse it for useful information with ease. Additionally, by not enabling logging and monitoring to detect unauthorized access, there is no safeguard in place to notify users of intruders marauding through the bucket.
While there are a variety of policies S3 users should familiarize themselves with, performing regular permission audits by reviewing AWS IAM policies and bucket permissions can help safeguard against accidental data leaks.
We reached out to TechMeetUps to report the data leakage, but they issued no response to our inquiry. As serious as the security incident is, the S3 buckets misconfigurations have not been resolved, posing a significant security risk to private company files.
Comments